Connecting Alibaba Cloud to AWS with High Availability VPN
By Geoffrey Gao, Delivery Engineer II
This article discusses about a high availability VPN solution for connecting AWS VPC to Alibaba Cloud VPC network, with traffic being directed through the Internet. Users with accounts in both AWS and Alibaba Cloud can make a secure and high availability VPN connection to achieve a multi-cloud architecture.
The article is intended for IT engineers, network administrators, or software engineers who already have a basic understanding of AWS and Alibaba Cloud VPC network components, and familiar with VPN technology for connecting two isolated private network.
This document do not cover the best practise for IPv6.
We will be using AWS VPN Gateway and strongSwan project to build the VPN connection.
Prerequisites
You should have:
- A certain familiarity with AWS and Alibaba Cloud
- Good understanding of the principles of networking, from setting IP addresses and firewalling by iptable tool
- Knowledge of the basic concepts of authentication based on public-key cryptography and a public-key infrastructure (PKI)
Specifically, I’m assuming that you have a VPC in each cloud, with the following configurations
- Non-overlapping networks in each VPC
- Public (and optionally private) subnets
- A routing table to route internet traffic for your public subnets via an Internet interface
- Appropriate security groups and attachments
High Availability VPN Connection between Alibaba Cloud and AWS
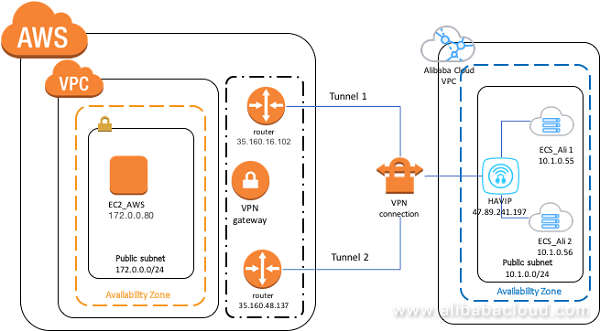
As we are going to connect a VPC in AWS to a VPC Alibaba Cloud to set up a multi-cloud infrastructure, we need to plan the network IPv4 CIDR block ahead to avoid the address block overlapping by these two VPCs. The architecture is shown below:
Configure strongSwan Servers in Alibaba Cloud
Configure two strongSwan servers in Alibaba Cloud VPC (vpc_ali)
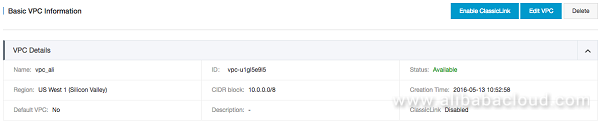
For this discussion, we shall assume that vpc_ali is located in us-west-1 and has a network block of 10.0.0.0/8.
Create a VPC on Alibaba Cloud with CIDR of 10.0.0.0/8 (vpc_ali)
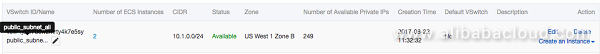
Create a public subnet in the vpc_ali with CIDR of 10.1.0.0/24
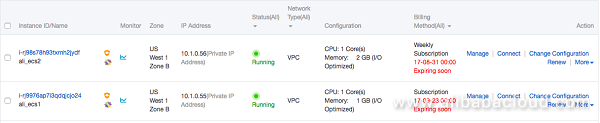
Launch two new ecs.n4.small instance in the public subnet of Alibaba Cloud VPC without default EIP attached.
Choose a CentOS 7u2 x86_64 Image
For now, ensure that your Security Groups are configured to permit SSH from your local workstation. We’ll need to reconfigure them later once both endpoints have been created.
Attach a new EIP to each the instance
Create a HAVIP address in the subnet with IP of 10.1.0.1 and associate to an EIP.
SSH to the two ECS instance and install StrongSwan and its dependencies:
$ sudo yum install –y strongswanEnable IP forwarding by doing the following as root
$ echo 1 > /proc/sys/net/ipv4/ip_forward && sudo sysctl –pInstall Keepalived server in these two ECS instance
$ yum install –y keepalivedConfigure keepalived in Master(ali_ecs1) and in Slave(ali_ecs2)
$ sudo echo 'systemctl start keepalived.service' >> /etc/rc.d/rc.local
$ mkdir /etc/keepalived/script
$ cd /etc/keepalived/script
$ vi notify.shIn the notify.sh file, add the following content.
#!/bin/bash
ENDSTATE=$3
NAME=$2
TYPE=$1case $ENDSTATE in
"MASTER")
echo "MASTER; `date`" >> /tmp/log
sysctl -w net.ipv4.ip_forward=1
iptables -t nat -A POSTROUTING -d 100.64.0.0/10 -j RETURN
iptables -t nat -A POSTROUTING -s 10.0.0.0/8 ! -p vrrp -j SNAT --to-source 10.1.0.1
systemctl restart strongswan.service
;;
"BACKUP")
echo "BACKUP; `date`" >> /tmp/log
iptables -t nat -F
systemctl stop strongswan.service
exit 0
;;
"FAULT")
echo "FAULT; `date`" >> /tmp/log
iptables -t nat -F
systemctl stop strongswan.service
exit 0
;;
*) echo "unknown state ${ENDSTATE} for VRRP ${TYPE} ${NAME}"
exit 1
;;
esac
Save and exit the vi editor, and run the following commands:
$ chmod +x notify.sh
$ vi ../keepalived.confThe priority item of the Master need to be larger than the Slave, so you will need to change some of the configurations when you configure in a Slave server. This includes the state, priority number, virtual_ipaddress, unicast_src_ip, and unicast_peer
! Configuration File for keepalivedglobal_defs {
notification_email {
acassen@firewall.loc
failover@firewall.loc
sysadmin@firewall.loc
}
notification_email_from Alexandre.Cassen@firewall.loc
smtp_server 192.168.200.1
smtp_connect_timeout 30
router_id LVS_DEVEL
}vrrp_instance VI_1 {
state MASTER
interface eth0
virtual_router_id 51
priority 150
advert_int 1
authentication {
auth_type PASS
auth_pass 1111
}
virtual_ipaddress {
10.1.0.1 dev eth0 label eth0:havip
}
notify /etc/keepalived/scripts/notify.sh
unicast_src_ip 10.1.0.55
unicast_peer {
10.1.0.56
}
}
Run the following command to start the service:
$ sudo systemctl start keepalived.serviceConfigure Routing
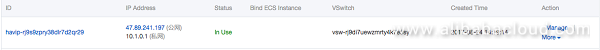
Navigate to your VPC console and bind the HAVIP to the two ECS instances:

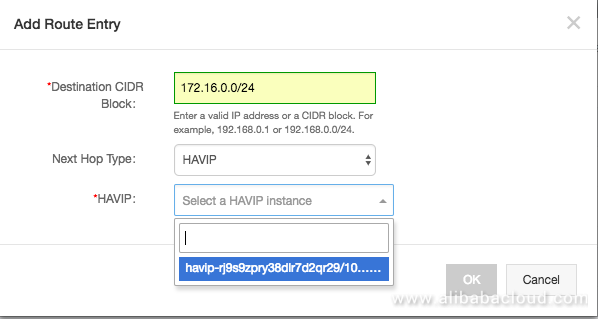
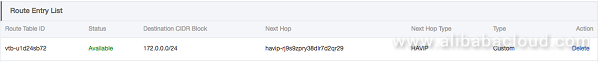
We need to tell our VPCs how to route to AWS by VPN server with HAVIP bound, so we add a route rule in VRoute configuration:
Configuring AWS
Having created two strongSwan ECS instances with a known public HAVIP address, it’s time to create the other end of our tunnel in AWS VPC. For this discussion, we shall assume that vpc_aws is located in us-west-2 and has a network block of 172.0.0.0/16.
A VPC on AWS with CIDR of 172.0.0.0/16 (vpc_aws)

A public subnet in the VPC with CIDR block of 172.0.0.0/24
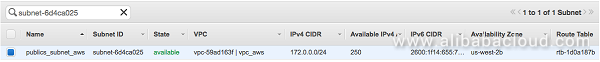
it has a route table item of 0.0.0.0/0 route to internet gateway

Configure AWS VPN gateway for connecting to Alibaba Cloud,
- Navigate to the VPC Dashboard in the AWS Console
- Make sure you are in the correct region(us-west-2)
- Select the ‘Virtual Private Gateways’ menu item
- Click ‘Create Virtual Private Gateway’
- Give your new VGW a name
- Select ‘Yes, Create’
- Once your VGW has been created, select it, and then click ‘Attach to VPC’
- Select the target VPC from the VPC drop-down list
- Select the ‘Customer Gateways’ menu item
- Click ‘Create Customer Gateway’
- Give your CGW a name
- Set routing to Static
- Set the public IP address of the remote end of the VPN connection, i.e. the VOIP of the Alibaba Cloud strongSwan instance.
- Click ‘Yes, Create’
- Select the ‘VPN Connections’ menu item
- Click ‘Create VPN Connection’
- Name: Give your VPN connection a name
- Virtual Private Gateway: Select the VGW you created in step 4
- Customer Gateway: Select ‘Existing’ and choose the CGW you created in step 8
- Routing Options: Static
- Static IP Prefixes: Set the CIDR block of your VPC you wish to make available over the VPN tunnel, e.g. 172.0.0.0/16 for the entire VPC network
- Click ‘Yes, Create’
VPN Connections:
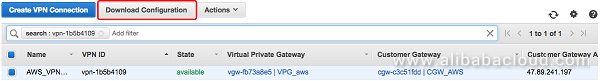
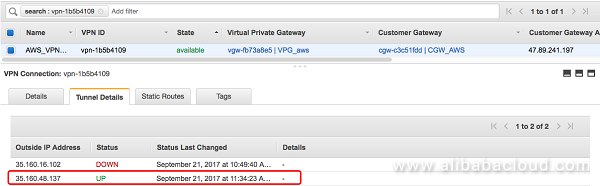
There two VPN tunnel created:

Once the VPN has been created, right-click on the entry and select the option to download the configuration file. Select the generic configuration option. This will save a text file to your local workstation with the information that will be needed to configure the strongSwan instance in the Alibaba Cloud VPC.
Now SSH to Alibaba Cloud ECS instances to configure strongSwan tunnels. Open the strongSwan IPSec file and edit it:
$ vi /etc/strongswan/ipsec.confConfigure the file as follows:
# Add connections here.
# Sample VPN connections
conn %default
ikelifetime=28800s
keylife=3600s
rekeymargin=3m
keyingtries=3
dpddelay=10s
dpdtimeout=30s
authby=secret
mobike=no
conn toawstunnel1
keyexchange=ikev1
left=10.1.0.55
leftsubnet=10.1.0.0/24
leftid=47.89.241.197
right=35.160.16.102
rightsubnet=172.0.0.0/24
rightid=35.160.16.102
dpdaction=restart
auto=route
esp=aes128-sha1-modp1024
lifetime=3600
ike=aes128-sha1-modp1024
ikelifetime=28800s
type=tunnelconn toawstunnel2
keyexchange=ikev1
left=10.1.0.55
leftsubnet=10.1.0.0/24
leftid=47.89.241.197
right=35.160.48.137
rightsubnet=172.0.0.0/24
rightid=35.160.48.137
dpdaction=restart
auto=route
esp=aes128-sha1-modp1024
lifetime=3600
ike=aes128-sha1-modp1024
ikelifetime=28800s
type=tunnel
Configure the secret keys /etc/strongswan/ipsec.secrets
47.89.241.197 35.160.16.102 : PSK "put_your_PSK_here_xxxxxxxxxxxxxxxxxxxx"
47.89.241.197 35.160.48.137 : PSK "put_your_PSK_here_xxxxxxxxxxxxxxxxxxx"Restart strongSwan and make sure the service is running.
$ systemctl restart strongswan.service
$ systemctl status strongswan.serviceTesting the VPN Tunnel
Now that we have both ends of the tunnel created, we need to ensure that they can talk to each other.
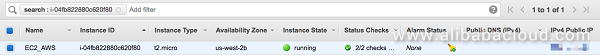
Create another Alibaba Cloud ECS and AWS EC2 instances in the corresponding subnet then SSH to the ECS instance and ping AWS EC2 instance by private IP address for an ICMP testing.

[root@ali_ecs_test ~]# ping 172.0.0.80
64 bytes from 172.0.0.80: icmp_seq=1 ttl=63 time=26.1 ms
64 bytes from 172.0.0.80: icmp_seq=2 ttl=63 time=26.2 ms
64 bytes from 172.0.0.80: icmp_seq=3 ttl=63 time=26.0 ms
64 bytes from 172.0.0.80: icmp_seq=4 ttl=63 time=26.0 ms
…Check the AWS VPN connection tunnel status on the console, the status of one of the tunnels already turn to UP.
Update Security Groups
Now, we’ll create a Security Group (or modify an existing one) to contain rules to permit the public traffic necessary to set up the IPSec tunnel. Configure your security group as per the table below.
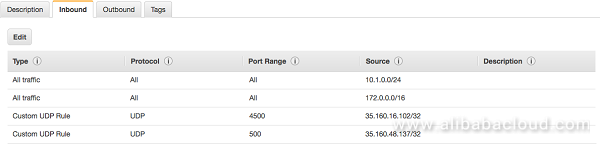
You don’t need to do anything particular on the AWS side to permit traffic; this was addressed implicitly behind the scenes when you created the Customer Gateway earlier on. You’ll just need to make sure that any security groups on either side of the tunnel explicitly allow traffic from the opposite network.
Conclusion
Hopefully you have been able to follow the steps above to bring up your own IPSec tunnel between Alibaba Cloud VPC and AWS VPC. AWS VPNs provide two tunnels for redundancy as AWS may perform maintenance on one of the tunnels from time to time. Having two established tunnels allows you to keep communicating over the VPN during these maintenance windows.
